With the recent rise of the topic of Security Access Service Edge (SASE), its application scenarios in the industry are constantly being explored. Recently, GoSDWAN encountered a scenario that was very suitable for using SASE when designing the basic network architecture for a real estate company.
Client J is a real estate company operating mid-to-high-end real estate in first- and second-tier cities. The sales department is a temporary sales office with luxurious decoration. But usually, after the project sales cycle is over, the entire office infrastructure is pulled. If an expensive end-to-end traditional private line service is used for it, not only the usage rate is low, but also the price is high, and the private line service cannot be terminated immediately after the end of the sales project. If the traditional network architecture construction ideas are adopted, unnecessary costs will be added to the operation of the project.

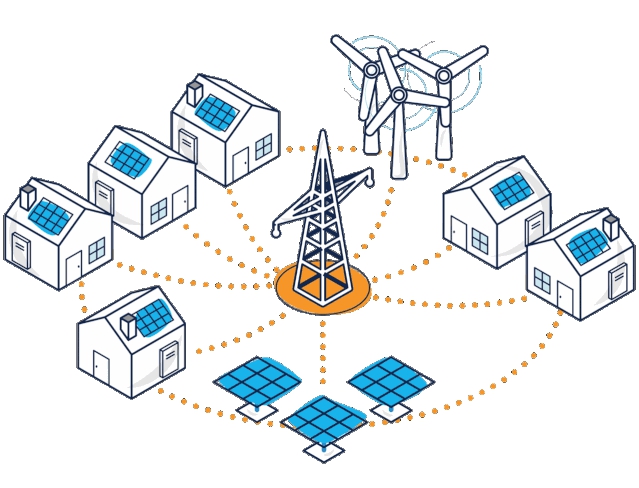
Therefore, during the design process, GoSDWAN considered setting up a Service Edge Node in a cloud-hosted manner for customers.
First, quickly deployed a cloud service gateway for J Company in the cloud where the sales department project is located;
Secondly, the sales terminal of the sales department uses the IPAD as the main business interaction tool. When the IPAD end connects to the above-mentioned cloud service gateway through VPN, all application traffic on the IPAD will be sent to the cloud service gateway through the whole station proxy.
Finally, behind the cloud service gateway is the UTM, WAF and other security filtering facilities built in NFV mode. After the traffic passes through the above facilities, the internal services such as network printers and internal network disks on the intranet can be presented in a relatively safe manner. At the same time, internal applications such as the CRM system, contract management system, and business approval query system associated with the sales end can also achieve high-quality access, and obtain more diversified security control elements to conduct security audits on data chain processing.
In addition to accessing the internal services of the enterprise, behind the cloud service gateway, the platform built on the cloud network adds the resources of partners to a unified and integrated data plane, such as the payment and settlement platform of the banking system, the credit reporting platform, and even the It is open business opportunity management, project management and other SaaS tools that can be controlled in one-stop, truly realizing the "front-line call for artillery fire".
Through the above practice, we can see that GoSDWAN's intelligent connection solution enables the thinking of the data transformation direction of traditional industries. Even the sales process of real estate companies can be informatized and digitized to realize intelligent business management. The data chain construction in traditional industries is point-to-point and decentralized, and new contradictions and wastes will be generated in both data decision-making and execution. Therefore, to open up the digital data chain, the key is to form an ecologically integrated digital underlying structure, break the data unknowability, instability and complexity in the traditional architecture, and realize timely visualization, perceptibility, and complexity in all ports of the data chain. Adjustable ability. Therefore, even if it is a front-line sales office setup, it is necessary to consider a set of underlying infrastructure that can be integrated, connected, used as it is built, and can be up and down. Through cloud-native computing power platforms, structural security management and building new application systems, demand perception, overall planning control, inventory management, process control, and capital allocation are integrated into a complete ecosystem to build a comprehensive ecosystem. A new decentralized partner system. Such a design, even if it jumps out of a edge computing real estate industry, is believed to be inspiring for sd wan manufacturing, cross-border e-commerce and service industries. Because whether it is new product development, flexible production or user management needs, the service edge built based on the security concept can make intelligent decisions and fully empower the front-line sales team. The digital and intelligently armed sales team holds a full set of digital toolkits to facilitate transactions and make optimal decisions.

The above GoSDWAN technical team has the following experience to share in the construction of such a practice:
Combined with SASE services, which have access rights based on user identity tags, the elements of security management are not only IP addresses, but the identities of users, network connections, and environments, so as to build differentiated and recognizable network interconnection experiences and access levels , quality of service routing, risk screening for application selection, and security audit policies.
Ideally, SASE services will be deployed using a cloud-native architecture without specific hardware dependencies, and can complete data chain construction independently, with third-party service chains only playing an additional role in enhancement. The advantage of software deployment is multi-tenant, Pay as you go, which maximizes hardware operating cost savings for customers. Rapid instantiation and the time effect brought about by the rapid expansion of services are also one of the important benefits of cloud native.
The SASE service is not only a connection, but also protects end devices, encrypts and decrypts inline traffic, etc. The cloud inner business side of the Service Edge is rich in computing power and algorithm engines. According to the orchestration of business policies, the inspection engine can also cover Secure Web Gateway (SWG), Security Information and Event Management (SIEM), Malware scanning, sandboxing, and more.
First of all, it needs to be determined that the network access is based on the identity of the user's device application and certificate. It is not based on the IP address or the physical location of the device. The user's device identity must reflect the business environment and not be associated with the upper-layer completely disjointed key structure. Binding identity to the network environment is the best way to enforce policy. In this way, dependencies on IP or applications can be eliminated, and security policies can be applied consistently regardless of where users and devices are located.
If only from the perspective of security audit, the provision of log management (LM, Log Management) plays a positive role in the professionalization and measurement of the business and the internal management of customers. On the other hand, as APT attacks (ie, advanced sustainable threat attacks, also known as targeted threat attacks) have received attention in the field of industrial Internet, the preservation of event trajectories and forensics in the operation of IT assets has become a security issue for many enterprises. Essential for reinforcement. In particular, SIEM is usually applied to the service chain on the business side only in large-scale systems or special industries.

With the deepening of industrial transformation, the innovative transformation of traditional enterprises has continued to iterate towards better cost, higher efficiency and more refined management. GoSDWAN firmly believes that through the integration of intelligently connected data planes, it can solve the data fragmentation of enterprises and give full play to the value of data in enterprise scenarios. Especially in the case of the normalization of the epidemic, it uses the rapidly built service edge solution to continuously provide services for the field employees of enterprise customers. In terms of continuity, in-depth practical exploration has been carried out.